Thursday, December 15, 2005
Tuesday, December 06, 2005
Knowing Microsoft, you'd bet on the former.
But on the other hand.. do they really believe this stuff? Entitled "The Internet Services Disruption", the memo paints Microsoft as a prescient innovator. For example. When we reflected upon our dreams just five years later in 1995,
the impetus for our new center of gravity came from the then-nascent
web. With a clear view upon the challenges and opportunities it
presented, the entire company pivoted to focus on the internet to
pursue that fully connected dream with support for internet standards
throughout our product line: a web browser, server and development
tools, and a service in MSN that was transformed into a web portal.
Many things we developed in that era continue to fuel the growth
of todays internet: the technologies of AJAX DHTML and XMLHTTP
were created in 1998 and used in products such as OWA.
Microsoft releases Windows Server 2003 R2 update: "
(InfoWorld) - Microsoft Corp. Tuesday released to manufacturing a long-awaited interim update to the current version of Windows Server OS, Windows Server 2003 R2.
The update, which will be generally available to customers in about 60 days, should be 100 percent compatible with applications running on the current release of Windows Server 2003, said Bob Muglia, senior vice president for server and tools at Microsoft, in a webcast Tuesday morning. 'If you have deployed Windows 2003 today you can feel confident deploying this without a long test cycle,' he said.
Microsoft released the first preview of Windows Server 2003 R2 in August and another preview in October.
Virtualization is a key focus of the update, which is designed to work closely with Virtual Server 2005, Microsoft Operations Manager (MOM) and Systems Management Server (SMS) as part of Microsoft's Dynamic Systems initiative, Muglia said.
Microsoft recently simplified its virtualization licensing for Windows Server System, of which Windows Server, MOM and SMS are a part. The company no longer requires a customer to pay for inactive or stored virtual images of Windows Server System on a network. Instead, Microsoft now only charges for the virtual images of Windows Server System products actually running on a customer network.
Microsoft also enables customers to have four virtual machines running on top of Windows Server 2003 R2 Enterprise Edition and Windows Server 'Longhorn' Datacenter Edition at no extra cost.
As part of its continued focus 'to take a leadership role in virtualization,' Muglia said Microsoft is offering a special promotion for Windows Server 2003 R2. Customers who purchase the enterprise edition of the update with get Virtual Server 2005 R2 Enterprise Edition for US$99 until June 30, 2006, he said.
The new Windows Server release also includes a key identity management technology for the company, Active Directory Federation Services (ADFS), which introduces the idea of federated network identity into the OS, Muglia said. This enables companies to securely provide distributed identification, authentication and authorization for users across organizational and platform boundaries.
In addition, Windows Server 2003 R2 also promises new branch-management capabilities; better Unix interoperability through the inclusion of the Unix subsystem within Windows; and a new version of the .Net framework, .Net 2.0, Muglia said.
Sunday, December 04, 2005
iPhoto 5.0.x: Solution for sharing photo libraries between multiple users: "Several MacFixIt readers have recently noted difficulty with sharing iPhoto libraries between multiple users of the same machine.iPhoto 5.0.x: Solution for sharing photo libraries between multiple users.
Several MacFixIt readers have recently noted difficulty with sharing iPhoto libraries between multiple users of the same machine."My wife and I each have our own login for our iMac. As such, I set up iPhoto to store files in the shared directory. Unfortunately, ComicLife did not like this and I had to move our iPhoto directory to my side of the Mac and then had an alias so my wife could still use iPhoto. This seem to work except I've run into the problem that if my wife uses iPhoto and then I use iPhoto later, the photos won't load for me (my wife can still load the photos on her side). Investigating a little further showed me that the permissions of a couple of those database files had been changed so that only my wife could read the files and in fact she was now the owner of those files. Fixing the permissions allowed me to once again load iPhoto. However, the problem has just happened again so I don't know what is going on."
IE bug lets hackers phish with Google Desktop: "An Israeli hacker has demonstrated how a bug in Microsoft's Internet Explorer Web browser can be used to steal personal information from Google Desktop users.DECEMBER 02, 2005 (COMPUTERWORLD) - A bug in Microsoft Corp.'s Internet Explorer Web browser gives phishers a way to scan the hard drives of Google Desktop users, according to an Israeli hacker. Because of a flaw in the way Internet Explorer processes Web pages, a malicious Web site could use the attack to steal sensitive information such as credit card numbers or passwords from the hard drives of its visitors.
"Google Desktop users who use IE are currently completely exposed," hacker Matan Gillon said via e-mail. "An experienced attacker can covertly harvest their hard drives for sensitive information such as passwords and credit card numbers. Since Google also indexes e-mails which can be read in the Web interface itself, it's also possible to access them using this attack."
Gmail virus scanning draws some user complaints: "
(InfoWorld) - The virus-scanning feature Google Inc. added to its Gmail Web mail service this week has generated concern, bewilderment and disappointment among some users.
The three main complaints being aired in Gmail discussion groups are: The virus-scanning feature can't be turned off.Gmail's long-standing virus protection -- blocking all executable file attachments -- will remain in place. Finally, Google isn't saying which vendor is providing the antivirus technology.
A Google spokeswoman said that, while Google gives thoughtful consideration to user feedback, for now it has no plans to make the antivirus feature optional, nor does it plan to stop blocking executables. She also declined to identify the source of the antivirus technology Google is using.
Disabling the virus scanning is convenient for users who may occasionally need to mail an infected file for reporting purposes to an antivirus vendor and for users who may regularly handle infected messages if they are, say, IT professionals involved in antivirus work.
William Boyle, principal software engineer at Brooks Automation Inc. in Chelmsford, Massachusetts, doesn't foresee being very inconvenienced, but he thinks Google should give users the option to turn off the feature.
'I just do not like to lose control over what I can send and/or receive,' Boyle wrote in an e-mail interview with IDG News Service. 'This may be a problem if I am trying to report a virus to someone.'
'I am a systems software engineer and must be able to send and receive any sort of message,' added Boyle, who has been using Gmail for about six months, but not as his primary account for work or personal communications.
Meanwhile, there are users feeling disappointed that Google is keeping in place its policy of blocking all executable file attachments in Gmail. Prior to the new virus-scanning feature, this had been Gmail's virus protection method.
One of these users is Thomas Quinlen, an attorney with McNabb, Bragorgos & Burgess PLLC in Memphis, Tennessee. 'With virus scanning in place, the blocking is redundant,' he wrote in an e-mail interview.
Quinlen, who uses Gmail as his primary e-mail account for personal communications, has felt inconvenienced by this feature whenever he has wanted to e-mail himself an application from one of his computers in order to install it in one or both of his other computers.
He has remote access to his work desktop PC from his laptop and from his home PC, he explained. 'But if I am going to be disconnected from the Internet -- on an airplane, for instance -- I need the [work] application on the other [nonwork] computer,' he wrote. 'Given the size of attachments Gmail allows, it seems like executables should be allowed, particularly if I am e-mailing it to myself, which is really just file storage rather than sending it out over the Internet.'
Although some technically savvy users are chiming in discussion groups with ways to disguise executables and trick Gmail into allowing them, Quinlen doesn't feel he has the necessary know-how to accomplish this. 'I doubt I have the computer skills to even attempt to defeat [this feature],' he wrote.
Finally, a number of Gmail users are loudly wondering in discussion group threads which antivirus technology Google is licensing, as they weigh what they perceive to be the strengths and weaknesses of different vendors. The consensus among these users is that they shouldn't be in the dark regarding which antivirus company is ultimately protecting their computers.
IE bug lets hackers phish with Google Desktop: "
(InfoWorld) - A bug in Microsoft Corp.'s Internet Explorer (IE) browser gives phishers a way to scan the hard drives of Google Desktop users, according to an Israeli hacker. Because of a flaw in the way IE processes Web pages, a malicious Web site could use the attack to steal sensitive information like credit card numbers or passwords from the hard drives of its visitors.
'Google Desktop users who use IE are currently completely exposed,' wrote hacker Matan Gillon in an e-mail interview. 'An experienced attacker can covertly harvest their hard drives for sensitive information such as passwords and credit card numbers. Since Google also indexes e-mails which can be read in the Web interface itself, it's also possible to access them using this attack.'Gillon has posted an extensive description of how such an attack would work, along with a proof of concept exploit, on his blog at http://www.hacker.co.il/security/ie/css_import.html.
The IE bug concerns the way Microsoft's browser processes Web page layout information using the CSS (Cascading Style Sheets) format. The CSS format is widely used to give Web sites a consistent look and feel, but attackers can take advantage of the way that IE processes CSS to get Google Desktop to reveal sensitive information.
Hackers would first need to trick users into visiting a malicious Web site for the attack to be successful, Gillon said. The attack works with IE 6 and Google Desktop v2, but it may also work on other versions of Microsoft's browser, but it does not work with non-Microsoft browsers like Firefox or Opera, he said.
Users can nullify the attack by turning off JavaScript in their browsers, Gillon said. This can be done by disabling 'Active scripting' in IE's Internet Options menu. JavaScript is a popular scripting language used by Web developers to make their sites more dynamic.
Users need to be particularly wary of the Web sites they visit these days, because of a second unpatched IE vulnerability that could be used to take over a user's PC. Hackers posted sample code that exploited this problem over a week ago and Microsoft said that hackers are already using the code in attacks. As with the CSS problem, users must first be tricked into visiting a malicious Web site for this second IE bug to be exploited.
Some security experts believe that Microsoft is in the process of rushing out a patch to fix this problem before these attacks become more widespread. These attacks can also be avoided by disabling JavaScript in IE, or by using an alternative browser.
Microsoft executives were unavailable to comment on the CSS bug, but a spokeswoman for the company's public relations agency said the issue is being investigated. Microsoft is not aware of any attacks resulting from the hole, she said.
Thursday, December 01, 2005
Attackers targeting unpatched IE bug, Microsoft warns: "Microsoft issued a warning that attackers could exploit a critical unpatched bug in Internet Explorer, first reported in May, and take over a user's computer.News.)
The bug involves the way Internet Explorer processes the "Window()" function in JavaScript, a popular scripting language that Web developers use to make their sites more dynamic.
Microsoft's Windows Live Safety Center is now able to detect and remove the malicious software, Microsoft's advisory said.
The vulnerability affects Internet Explorer users on Windows XP, Windows 2000 and Windows 98, Microsoft said. "Customers who are running Windows Server 2003 and Windows Server 2003 Service Pack 1 in their default configurations, with the Enhanced Security Configuration turned on, are not affected," the advisory said.
News: Apple releases update for iPod Shuffle: "Apple on Wednesday released an update for the iPod Shuffle that, according to Apple, fixes some ‘bugs’ with that particular model. Apple did not specify what changes were made with the new software. iPod Updater 2005-11-17 includes iPod Software 1.1.3 for the iPod Shuffle. The update contains the same software versions as iPod Updater 2005-10-12 for all other iPod models. The 37MB download is available from the company’s Web site or via the software update control panel."
PDFKEY PRO 2.0 RELEASED BY ACUTUS TRADING
Vancouver, BC - 1 December 2005 - Acutus Trading today announces the release and immediate availability of PDFKey Pro 2.0. PDFKey Pro is a Mac OS X utility that unlocks and decrypts password-protected PDF documents. PDFKey Pro is designed to help Mac users work with PDF files even if their passwords have been lost. Version 2.0 contains usability and performance enhancements to this popular Mac utility.
Why Can't Microsoft Just Patch Everything?: "paneraboy writes 'If smaller software companies can patch all of their bugs serious or minor, ZDNet's George Ou asks, why can't Microsoft -- with its massive army of programmers and massive budget -- patch all of its vulnerabilities? Had Microsoft fixed a low risk browser vulnerability six months ago, perhaps we could have avoided last week's zero-day exploit. Currently, more than two dozen Windows XP issues remain unpatched. Ou thinks Microsoft ought to fix them all.' From the article: 'Almost 4 years after the launch of Trustworthy Computing, I found myself wondering why am I staying up till 4:00 AM to deliver an emergency set of instructions (Home and Enterprise) to my readers because Microsoft felt it unnecessary to patch a flaw six months ago that was originally low risk but mutated in to something extremely dangerous.
EU ministers approve biometric ID, fingerprint data sharing: "
All this and record retention too!
The European biometric ID card takes another step forward this week, with the European Justice and Home Affairs Council set to approve 'minimum security standards' for national ID cards. Alongside this the Council will be roadmapping the rollout of Europe's biometric visa system, which will contain the fingerprints of 70 million people within the next few years, and hearing European Commission proposals for greater sharing of fingerprint data.
There is a major bug in Firefox where if you hold down the mouse button to select text, or scroll, or anything inside the browser window, the Firefox CPU usage shoots up to nearly 100% and hogs your entire system until you let go. I just tested it using top and can verify that the CPU usage jumps to between 75-95% depending on the other applications in use at the time. For Powerbook or iBook users this is a major issue, considering your fans will probably turn on and you'll battery will drain much quicker.
Sunday, September 25, 2005
Adobe CEO says bloated Microsoft has no heart: "
Our publishing empire is safe
The pressure of competing with Microsoft appears to be getting to Adobe's boss. Its CEO Bruce Chizen today lashed out at his former employer, describing Microsoft as a bloated, heartless empire. Chizen, speaking at a Churchill Club event here at the Computer History Museum, at first tried to avoid any direct attacks against Microsoft, even though he was tossed a softball question about the apparent reasons behind Microsoft's recent executive reorganization. Many pundits painted the executive shuffle as Microsoft's admission that its corporate structure had become inefficient and inadequate. Adobe's CEO, however, wouldn't be drawn.
US deploys satellite jamming tech: "
Son of Star Wars tracks phantom menace
The US has created electronic-warfare squads capable of jamming enemy satellite transmissions. Fearful of losing its advantage of superior technology resources over its potential enemies, the US has established mobile teams equipped with electronic jamming gear capable of disrupting attempts to interfere with its satellite resources,
Friday, September 09, 2005
Will the Newton Ever Come Back? Why should it? When all the PDAs are slowly dying?: "
Why don’t we take a trip back down memory lane for a moment shall we? Many of us will remember back to our first kiss and how sweet a kiss it was! Some of us might go back to when big hair was still in style or when Michael Jackson wasn’t…"
(Via AppleMatters.)
Linux Five Years Away From Mainstream! Hard to believe! Not time wise - but the fact that someone would decide that Linux Must become Mainstream!: "wellington wrote to mention a ZDNet blurb about a Gartner group study. Gartner indicates that 'mainstream' use of open source in IT environments may be 5 years away. From the article: 'Gartner's latest Linux 'hype cycle' report shows that open source is halfway to maturity but warns the biggest test will be whether it can demonstrate the necessary performance and security to function as a data centre server for mission-critical applications. Leading-edge businesses are generally still in the early stages of Linux deployments but Gartner expects increased commercialisation and improved storage and systems management for the operating system by the end of 2005, with Linux being used primarily for WebSphere and infrastructure applications on mainframes and web services on blades and racks.
Firefox blighted by unpatched bug! So it is not all Sweets and Roses in the other camps, either!: "
IE-style security flap hits alternative browser
Security researchers have discovered an unpatched vulnerability in Firefox that might be used to crash vulnarable systems. Hackers might also use the security bug to trick surfers into running malicious code by simply fooling them into visiting a maliciously constructed website.…
Can you beleieve what type of Cheap phone the designated for this venture? ROKR: the World’s First Mobile Phone with iTunes: "Apple, Motorola and Cingular Wireless today announced the availability of the world’s first mobile phone with iTunes, enabling music lovers to transfer up to 100 of their favorite songs from the iTunes jukebox on their Mac or PC to their mobile phone. [Sep 07, 2005]"
(Via Apple Hot News.)
Saturday, September 03, 2005
Motorola-built iPod Phone next week? Not worth looking at, say pundits: "
User interface is the problem, not the solution
It's been an open secret for a while now that Apple wasn't going to let Sony Ericsson's 'Walkman phone' become a market leader in the new market for a combined music/comms toy. Word on the street says that the new phone/player will be announced next week, Sept 7th.…
"(Via The Register.)
Monday, August 29, 2005
Three indicted in U.S. spam crackdown: "Three people have been indicted in Arizona on federal charges of violating the antispam law."
I Love this! It is about damn time!
Three people accused of sending massive amounts of spam face possible prison sentences after being indicted by a grand jury in Arizona and accused of violating the Controlling the Assault of Non-Solicited Pornography and Marketing (CAN-SPAM) Act of 2003 and other charges, the U.S. Department of Justice said in a statement.
Named in the indictment are Jennifer R. Clason, 32, and James R. Schaffer, 39, of Arizona, and Jeffrey A. Kilbride, 39, of California. The three are accused of sending unsolicited e-mails that advertised pornographic Web sites, the Justice Department said in a statement. They could make money from commissions that the Web sites paid in return for directing traffic to their sites, the statement said.
Microsoft begins test of new Windows file system: "Blog: Microsoft on Monday posted the first test version of a new Windows file system. The company made the test version...
As I have suspected all along! MS will deliver most of the Vista's functionality by the time that it is released!
Zotob suspect under arrest: "Atilla Ekici is arrested in Turkey, under suspicion of having created both the Zotob and Mytob worms.Zotob suspect under arrest
Turkish police escort Atilla Ekici (center) to a court in Ankara, Aug. 26, 2005. Ekici is suspected of having created the Mytob and Zotob worms. A second suspect was arrested in Morocco.
Thursday, August 25, 2005
How Microsoft Will Die! Do you believe this?: "
Longhorn, by the features
WFS: Cut
.NET Framework: Cut
MONAD: Cut
Integrated Search: Cut
Avalon: Who knows?
Indigo: Who knows?
IE7: You can repaint a Kia, lower it down, put rims on it and think you are…"
Macintosh: Intel Inside! Now Improved With Delicious DRM: "
The story hit the ‘net with the all the raw fury of a F5 tornado reducing trailer park after trailer park to so much Formica and splinters of bad furniture. The event was, of course, the revelation that the developer builds of Apple’s forthcoming OS for the announced Macintels included…"
Polyglot IM worm targets MSN: "A new worm spreading over IM networks is the first to check system settings in order to send a message in the appropriate language. The Kelvir-HI instant messaging worm is spreading over MSN Messenger's network, albeit modestly. IM security specialist Akonix classifies it as a low-risk threat."
Wednesday, August 24, 2005
Phishers and security firms in malware 'arms race': "
Def Con
Conventional phishing attacks launched via spam messages are becoming eclipsed by sophisticated malware designed to steal identities, according to a study by Anti-Phishing Working Group (APWG). Conventional phishing attacks launched via spam messages are becoming eclipsed by sophisticated malware designed to steal identities, according to a study by Anti-Phishing Working Group (APWG). APWG's July 2005 phishing reports adds that fraudsters are developing approaches specially designed to neutralise counter-phishing technologies.
APWG researchers reported a "marked increase" in screenscraper technology by phishers, an approach designed to counter graphical keyboard systems sometimes used by banks to thwart conventional key-logging Trojans. When a consumer selects a character on the graphical keyboard using mouse clicks, the screenscraper takes a snapshot of the screen and sends it to the phishers' server, in one example intercepted by the researchers. Despite the emergence of this more sophisticated technique keylogging Trojans remain a popular option. There were some 174 phishing-based Trojans detected in July, up from 154 in June. The majority of these Trojans lay in wait on sites hosted in either Brazil or the US. APWG's July 2005 phishing reports adds that fraudsters are developing approaches specially designed to neutralise counter-phishing technologies.…
Intel announces 'desktrino' home PC platform: "
'East Fork' to go live as VIIV
IDF Talk about Capitalizing on A DEAD HORSE! Intel has announced it is to offer a 'desktrino' home PC platform. The Centrino-esque brand will be VIIV - pronounced 'vive, IDF Intel has announced it is to offer a 'desktrino' home PC platform. The Centrino-esque brand will be VIIV - pronounced 'vive'.
Unsurprisingly, it's founded on a dual-core processors, and it's based on Windows Media Center Edition, VP and General Manager of Intel's Digital Home Group, Don MacDonald, revealed at Intel Developer Forum today.
“Look, Ma, No Schoolbooks”: "Wired News reports, Will this Ever happen in our life time? ‘Students at Empire High School here started class this year with no textbooks — but it wasn’t because of a funding crisis. Instead, the school issued iBooks — laptop computers by Apple Computer — to each of its 340 students, becoming one of the first U.S. public schools to shun printed textbooks. School officials believe the electronic materials will get students more engaged in learning.’ [Aug 19, 2005]"
(Via Apple Hot News.)
Apple Earns PC Magazine Readers’ Choice Awards: "PC Magazine reports, ‘Once again, Apple achieves scores that are far and away the highest for all vendors in our survey, earning Readers’ Choices in both desktops and notebooks. For Apple, in both the desktop and notebook sections of the survey, every single score is significantly better than the industry average for Windows machines. No exceptions.’ [Aug 24, 2005]
Thursday, August 11, 2005
Oops
A glitch with IE updates available through Microsoft's Download Centre interrupted the smooth passage of Redmond's monthly patch express on Tuesday. The updates available on Microsoft Update and Windows Update were not affected and are installing properly but the files posted for manual download became corrupted. As a result their digital signature became broken and the patches failed to load properly.…
Girls prefer girly websites: official Like DUH! Didn't we know?: "
And blokes like it butch
A study by Glamorgan University Business School's Department of the Fairly Bleedin' Obvious has concluded that it's not just a website's subject matter that determines whether it appeals more to guys or gals but - wait for it - 'the appearance of the site also might play a subtle role', as AP explains.…
The enemy is all around
A Labour MP is calling for updated legislation and greater international co-operation to make it easier for police to track and trace terrorist recruiters, animal rights extremists and other criminals on the net. Margaret Moran MP, chair of all-party Parliament Industry group EURIM, said that the police 'urgently' need resources to find extremists who 'use the internet to ensnare those who are alienated from society and turn them from sympathisers into enthusiasts and then fanatics'.…
Television is joining the 21 Century, Kicking and Screaming! CNN Using iChat AV: "Macworld staff reports, ‘CNN has begun an experiment that uses iChat AV to conduct face-to-face interviews. A new US show hosted by Wolf Blitzer, ‘Situation Room’, aims to mix traditional reporting with new online technologies — such as iChat AV.’ [Aug 09, 2005]"
Thursday, August 04, 2005
Should The Mac Zealots Just Shut Up?: "
It is unlikely that there is any city in the US with a population over hundred thousand folks where you can’t go to central spot on a Friday evening and not receive the dreaded ‘attempted conversion.’ The procedure is both tiresome and familiar and runs something as follows: “You, in the black shirt, are you prepared for the end of the LIFE AS YOU KNOW IT!!!!!!?”
You: “I’m comfortable with my…”
Nut case: “Have you heard the WORD, the WORD will save you and this great country!!!!!?”
You (trying to be polite): “Uh, like I said, I’m fairly comfortable with my current choice in the…”
Nut Job: “Friend, allow me to give you this pamphlet. The PAMPHLET will open your eyes to the EVIL around US. SON, read the PAMPHLET and spread the WORD!!”
You: “I’m open minded, but I find your tactics not only annoying but a bit disingenuous so…”
Total freakin Nut Case: “Behold one of the EVIL ones, one the scorned few who drive four bangers. One who openly rejects the liberating advantages of a FULLY HEMI POWERED ENGINE. Scorn him children. Scorn the fool!”
You: “ Please tell me you won’t be here when I come out the bar.”
Person teetering betwixt institutionalization and self-care: “Will you please donate a few dollars so I can continue to spread the good WORD about the awesomely powered HEMI ENGINES!!!!?”
You: “Here’s two bucks”
We believe that the company will attempt to disrupt the Xbox 360 launch with a price cut, and as a result may succeed in diverting attention away from the higher priced next generation console. We expect the Microsoft to attempt to engineer the Xbox 360 to be compatible with the current generation Xbox, and as a result, believe that Microsoft will maintain $149 pricing for its money-losing hardware..'
Windows Vista Tool Targeted By Virus Writers: "An anonymous reader writes 'Five proof-of-concept viruses that target Monad, the next version of Vista's command prompt, have been published on the web. Monad is a command line interface and scripting language that is similar to Unix shells such as bash, but is based on object-oriented programming and the .Net framework. The viruses' only action is to infect other shell scripts on the host's operating system. They would cause little harm in the wild, but would be relatively easy to modify using the information from the article, said Mikko Hyppönen, the director of antivirus research at F-Secure.'
Sunday, July 31, 2005
Where for art thou, Brushed Al?: "
Why has Apple forsaken the Brushed Aluminum skin? And Aqua for that matter?
Using Tiger, I’ve gotten used to the somewhat bland, Windowsish look. But the other day I fired up Onyx and was immediately struck by how stunning it looked. Here’s a snapshot:
Whether you liked Brushed Al or not, when someone from the dark side saw it, they knew they were looking at something with a bit of class.
Is your printer spying on you?: "
Tech tracking spooks EFF
Secret codes enbedded into pages printed by some colour laser printers pose a risk to personal privacy, according to the Electronic Frontier Fundation. The US privacy group warns the approach - ostensibly only designed to identify counterfeiters - has become a tool for government surveillance, unchecked by laws to prevent abuse.…
All this sounds like the stuff of black helicopter conspiracy theory but the EFF wants to flesh out its preliminary research by gathering information about what printers are revealing and how. It's asking consumers to get involved by sending in test sheets from colour laser printers. In addition to documenting what printers are revealing, the EFF is filing a Freedom of Information Act (FOIA) request over the issue. These research efforts are a necessary precursor to any legal challenge from the EFF and ammunition for possible lobbying on legislation to protect consumer privacy.Wednesday, July 27, 2005
Disney, DreamWorks, Pixar Go Linux: "robinsrowe writes 'Most of the major studios use Linux -- such as DreamWorks with more than 1,500 Linux desktops and 3,500 Linux servers. The MovieEditor Conference is an all-day event on computer-based filmmaking in downtown Los Angeles on August 3rd. Studio technology chiefs and other experts discuss ongoing work using Linux in feature animation and visual effects. Presented in collaboration with LinuxMovies.org.'"
(Via Slashdot.)
VoIP Security: "An anonymous reader writes 'Whitedust are running an interesting article on the security aspects of VoIP. From the article: 'The fact that VoIP operates across standard networks makes it vulnerable to all manner of IP hacking - including man in the middle attacks,sniffing, session hijacking, etc.' Considering it's recent growth, how secure is VoIP?' PCM2 sent us a wired bit about Phil Zimmerman of PGP working on a privacy system for Voice over IP calling"
(Via Slashdot.)
Personal storage sites are a 'safe haven for hackers': "
Censorware firm apes Mary Whitehouse
Websense, the employee management software outfit that's become best known for heaping FUD on emergent net technolgies, has found a new target. Hot on the heels of charecterising online storage sites as a conduit for industrial espionage and blogs as a host of malware it's decided to chastise personal web hosting sites as a 'Safe Haven for Hackers'.…
Sunday, July 24, 2005
What OS X Could Learn From Windows: "
Okay.
Hard hat? Check.
Flak jacket? Check.
Flame proof vest? Check.
White flag? Check.
Deep breath? Check.
Windows has some features OS X could do with.
There, I said it. Nice and quick and up front. No…"
1) Compatible control keys.
2) Save button on toolbars.
3) A multi button mouse.
4) Only show relevant file types in open and save dialogs.
5) Sort folders to top of directory listings
6) More context sensitive help.
Read More ...
Wednesday, July 20, 2005
Next: Video on the go on the Apple iPod?
Speculation is that videos, downloaded from iTunes, will be the next apple of iPod's eye. But if you think carefully about it, you will find it strange. You need a much larger Color LCD than any Model of iPod has at this time. Now there is also the idea of a bigger battery and more complex man board / CPU. So how much bigger this creature will be? We have to wait and see!
Tuesday, July 19, 2005
400,000 Windows users switch to Mac
Then they say that there are not switchers. LOL! Where there is. As for me, I will never switch, you know why? I use both, and that is the smart thing to do.Apple passes Lenovo in U.S. computer sales
Apple Computer moved up a notch to become the No.4 seller of personal computers in the United States in the second quarter as Macintosh sales soared by one-third, according to two reports. Lenovo, the Chinese company that owns the IBM personal computer brand, lost share.
This is Significant!
Monday, July 18, 2005
AGOS (Reuters) - A Nigerian court has sentenced a woman to two and half years in jail after she pleaded guilty to fraud charges in the country's biggest e-mail scam case, the anti-fraud agency said on Saturday.
Amaka Anajemba, one of three suspects in a $242 million fraud involving a Brazilian bank, would return $48.5 million to the bank, hand over $5 million to the government and pay a fine of 2 million naira ($15,000), the agency said.
Scams have become so successful in Nigeria that anti-sleaze campaigners say swindling is one of the country's main foreign exchange earners after oil, natural gas and cocoa.
What is Next for iPod? Is apple planning to come up with an Egg Beater version as well? Video iPod May Arrive in September: "Fuzzball963 writes 'MSNBC is reporting that Apple is in talks with major record labels to license and sell video content on the iTunes music store. The videos would sell for $1.99 and be playable on a video iPod, which Apple has reported may come out sometime in September.' Update: 07/18 18:54 GMT by T : Carl Bialik from the WSJ writes 'Just to add to the previous Apple post, here's a free link to today's Wall Street Journal article upon which the MSNBC article was based.'"
Monday, July 11, 2005
All our Prayers are with them! Go NASA GO! Shuttle is go for launch: "
In the absence of any lightning
The Shuttle Discovery is good to go, NASA says, and is on standby for launch later this week, despite Hurricane Dennis having slammed into the Florida coast. Weather forecasters say that there is a 30 per cent chance of weather disrupting the launch, according to NASA. Frankly, those are better odds that you'd get on most English picnics going ahead.…
Sunday, July 10, 2005
Pocket PC VS Palm Showdown: "Espectr0 writes 'TuxTops has a small review comparing the Pocket PC handhelds against the Palm ones (no pun intended), with advantages and disadvantages of each. The conclusion? If you are after gaming, multimedia, good WiFi+Bluetooth support, a lot of accessories and versatility, go with Pocket PC. If you are after small and stylish devices with good battery life, simple interface and simple PIM apps, go with PalmOS.'"
Saturday, July 09, 2005
Friday, July 08, 2005
Are We too Late? Has Intel taken over? IBM Officially Unveils Dual-core PowerPC Chips: "PM4RK5 writes 'Today at the Power Everywhere Forum in Japan, IBM officially unveiled its rumored dual-core PowerPC line of chips, the 970MP. Code-named Antares, these chips have been rumored to be under development since 2004. It is believed that Apple has been working with prototypes and is likely to use them in forthcoming updates to the PowerMac G5 line. The press release is in Japanese; as of this writing, IBM has not released an English version. Some of the slides from the presentation given by IBM are available. The processors pack some impressive specs, ranging from 1.4 to 2.5 GHz and including 1MB L2 cache per core; the chips also include the ability to power down the extra core when it is not needed. Alongside the 970MP, IBM also announced its low-power 970FX chips, ranging from 1.2 to 1.6 GHz, with power consumption ranging from 13 to 16 Watts, respectively.'"
POWERアーキテクチャーに更なる弾み Power.orgの新メンバー、OpenPower Projectの拡大、Power新製品を発表 BM®は本日、東京で開催された「Power Everywhere™ Forum 2005」において、Power Architecture™関連の新製品、パートナー、イニシアティブを発表し、引き続きIBM POWER™ マイクロプロセッサー・ファミリーの世界的展開に弾みをつけていくことを示しました。(If you can translate it!)
Apache Request Smuggling Vulnerability Found: "An anonymous reader writes 'Whitedust is reporting on a HTTP request smuggling vulnerability in Apache. The flaw apparently allows attackers to piggy back valid HTTP requests over the 'Content-Length:' header, which can result in cache poisoning, cross-site scripting, session hijacking and other various kinds of attack. This flaw affects most of the 2.0.x branch of Apache's HTTPD server.'" Extract:
All versions of Apache previous to 2.1.6 are vulnerable to a HTTP request smuggling attack which can allow malicious piggybacking of false HTTP requests hidden within valid content. This method of HTTP Request Smuggling was first discussed by Watchfire some time ago. The issue has been addressed by an update to version 2.1.6.
The vulnerability involves a crafted request with a 'Transfer-Encoding: chunked' header and a 'Content-Length' can cause Apache to forward a modified request with the original 'Content-Length' header. The malicious request may then piggyback with the valid HTTP request possibly resulting in cache poisoning, cross-site scripting, session hijacking and other various kinds of attack. This vulnerability has resurfaced due to vendor confirmation, the original Watchfire Whitepaper on HTTP Request Smuggling is here.
(Via Slashdot.)
Sunday, July 03, 2005
Was Apple coerced into Intel partnership?: "The consensus is that there would have been 'no sense' in Apple looking at alternative AMD processors. Analysts are wondering whether Apple was coerced into working with Intel, following AMD's lawsuit against the microprocessor company. However, the consensus is that there would have been "no sense" in Apple looking at alternative AMD processors."
Friday, July 01, 2005
Will this Nightmare ever End?
SCO Versus Novell Going All the Way: "Robert writes 'Computer Business Review reports that ownership of the Unix System V code copyrights is set to be decided in court after a US District Judge rejected Novell Inc's second request that SCO Group Inc's slander of title case be dismissed.' From the article: 'Novell's second motion to dismiss SCO's slander of title claim was prompted by an apparently positive response from Judge Dale Kimball to its first request to throw out the case, although he rejected it having concluded that the arguments about the agreements at the heart of the case would be more properly heard on potential later motions for summary judgment or trial.'"
(Via Slashdot.)
Thursday, June 30, 2005
The 12-minute Windows Heist: "An anonymous reader writes 'Sophos has come up with some pretty interesting research: apparently, there's a 50 percent chance unprotected Windows PCs will be compromised within 12 minutes of going online. Sophos came to that conclusion based on research covering the last six months of virus activity. The company said authors of malware such as spam, viruses, phishing scams and spyware have increased both the volume and sophistication of their assaults, releasing almost 8,000 new viruses in the first half of 2005 and increasingly teaming up in joint ventures to make money. The new-virus figure is up 59 percent on the same period last year.'"
Wednesday, June 29, 2005
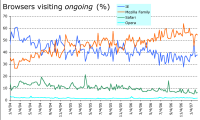
Almost every Sunday I grab the weeks ongoing logfiles and update my browser market share readout. I find it interesting and maybe others will too, so this entry is now the charts permanent home. Ill update it most weeks, probably. [Updated: 2005/06/26. Hey, hows this: suppose I did browser market shares only for people who come here as the result of a search. Intuition says that that would be a number much closer to the mainstream. Ill run some numbers and lets see.]...
AMD Moaning and groaning, or the Big Bad Intel has been naughty? News: AMD files broad antitrust suit against Intel: "Semiconductor maker AMD has filed an antitrust suit against rival Intel, just as Apple has announced plans to switch its computers to an Intel-based architecture."
It seems that Microsoft is trying to catch up by integrating RSS features into IE7 that are already available in Safari and Firefox. A beta version of IE7 is to be released later this summer, and an article at PC Mag shows the new RSS features that are to be added in IE7 and Longhorn. Today, Microsoft announced that it will introduce new technologies designed to promote the use of Really Simple Syndication, or RSS,
Tuesday, June 28, 2005
New worm lures users with 'breaking news': "
Internet users alarmed over news of Michael Jackson's death or dark conspiracies behind the demise of Pope John Paul II should perhaps just be worried that they received another new e-mail worm.Researchers at security firm Sophos warned Tuesday of the spread of the Kedebe-F e-mail worm, which carries a variety of subject headers and messages touting breaking news. However, users who click on the attached file could have their security software and firewall disabled, according to Sophos.
Possible messages include 'someone sent me this document which is stolen from a secret government body ... about John Paul's death.' Other messages try to entice recipients into opening the attached file by claiming Michael Jackson has died, Osama bin Laden has been captured by U.S. soldiers or the MyDoom e-mail worm author has been arrested by Microsoft, Sophos said.
Using supposed 'breaking news' to persuade users to open a message and click on an attachment is a long -favored method among virus writers, according to Sophos Senior Technology Consultant Graham Cluley.
'This is a fairly common trick. It doesn't take Albert Einstein to think this one up,' Cluley said.
Although the worm is currently slow-spreading Cluley flagged it as an example of the kinds of social-engineered threats that users should watch out for.
The worm spreads via e-mail or P-to-P (peer-to-peer) file sharing networks. It appears to be targeted at both news hounds and geeks, with mentions of the MyDoom worm, Cluley said. Also, it spreads on P-to-P networks by copying itself to the directory for sharing information on the server, purporting to be source code for the Sasser worm.
Apple today announced it is taking Podcasting mainstream by building everything users need to discover, subscribe, manage and listen to Podcasts right into iTunes 4.9, the latest version of its award winning digital music software and online music store. iTunes users can now easily subscribe to over 3,000 free Podcasts and have each new episode automatically delivered over the Internet to their computer and iPod.
News: Microsoft updates Virtual PC with Tiger fixes: "Microsoft has released its promised fixes for Virtual PC to work with Tiger."
Virtual PC 7.0.2 provides fixes for Virtual Switch, Zero Configuration Printing and the Dock Start menu when running on Tiger, according to Microsoft. The update works with Virtual PC 7.0 and 7.0.1. System requirements call for G3/700MHz or faster, Mac OS X v10.2.8 or later, 512MB RAM, 70MB hard disk space.
AMD speeds up single-core gaming chip: "
While dual-core processors have received the most attention this year, sometimes a single-core processor is the right tool for the job, according to AMD.The Sunnyvale, Calif., company is expected to release its fastest single-core processor on Monday with the launch of the Athlon 64 FX-57, a high-end chip targeted at gamers. The chip runs at 2.8GHz, a 200MHz increase in clock speed over the FX-55, which AMD will continue to sell for now, said Jonathan Seckler, product marketing manager for the Athlon 64 product line.
Both AMD and Intel sell high-end desktop processors that are very expensive and very powerful. AMD uses the Athlon 64 FX label for these chips, while Intel brands them the Pentium Extreme Edition. Neither company sells very many of these chips compared to sales of their mainstream desktop processors, but some users, such as gamers, are willing to pay whatever it takes to get the highest level of performance.
Saturday, June 25, 2005
Logitech Wireless Headphones for iPod: "No more tangles, snags or kinks: Now music lovers can free themselves from the cords tethering them to their iPod and receive high quality sound -- wireless headphones for the iPod(R) have arrived. Logitech a leading provider of cordless peripherals..."
I’ve been moving the TWiT web site - twit.tv or thisWEEKinTECH.com - to a new dedicated server. The idea was to put it on its own machine so it wouldn’t slow down leoville.com or leoville.tv (they’re on a shared server right now). leovilletownsquare.com has its own server.
The sites transferred over ok yesterday but something seems to be wrong today, and Vizaweb hasn’t been exactly responsive to my ‘emergency’ requests. Not sure what’s going on over there, but I’m looking for new hosting as quickly as possible and I hope we’ll have the site back up soon. Meanwhile watch this site for updates.
Sorry about this guys.
UPDATE: I’ve talked with Vizaweb and there’s not much we can do about it. It’s not a bandwidth issue - it’s an i/o issue. With 30 people per second hitting the site it’s just like a big DOS attack - except it’s real requests. You can help by using your podcasting client to get the latest TWiT episodes instead of trying to get them by hand. We’re going to find a host that specializes in this kind of traffic. Meanwhile the servers my other sites are running on are more than adequate, so I’ll keep them at Vizaweb. It’s just that TWiT is so much bigger than all the rest. The price of success I guess!
IBM ruffles workers by expanding India staff: "Leaked internal document shows big growth in Indian workforce due to 'shifting investment. With The New York Times reporting Friday on IBM's plans to significantly expand its staff in India while cutting jobs elsewhere, the company once again found itself balanced at the delicate intersection of global business realities and U.S. politics.'"
Friday, June 24, 2005
Sony denies seeking PSP customer data: "Company says it's targeting 'gray market' sellers rather than consumers to squelch unauthorized sales in the U.K.
I have no idea if this is true or not. But Sony never does anything without a motive, or do they?
Published reports out of Britain suggest that Sony is using the knowledge to confiscate any unauthorized product being shipped to consumers before the official launch date of Sept. 1.
CodeWeavers CrossOver To Support Intel-Based Macs: "mprindle writes 'Code Weavers produces software for Linux based machines that allows Windows software packages to run seamlessly. Code Weavers has announced that it will port it software to the new Mac's that will be running on Intel Processors. From the article at MacWorld'By installing CrossOver Office on Intel-based Macs, many Windows-only applications, including Windows-based games, utilities and business applications, will operate seamlessly and reliably,' No mention of expected performance in the article."
WebObjects 5.3 Update for Mac OS X Server 10.4 posted: "Apple has posted WebObjects 5.3 Update for Mac OS X Server 10.4 to its Web site today..."
(Via MacMinute.)
Sunday, May 22, 2005
Apple Msc OS X 10.4.1 Released!
Well it is here! OS X 10.4.1 has been released! Here is a short description of it:
It includes improvements for:
- file sharing using AFP and SMB/CIFS network file services
- using DHCP in wireless networks
- user login when accessing LDAP and Active Directory servers
- core graphics including updated ATI and NVIDIA graphics drivers
- synchronization with .Mac
- Address Book, iCal, Font Book, Mail, and Preview applications
- Dashboard widgets: Address Book, Flight Tracker, Phone Book, and World Clock
- compatibility with third party applications and devices
For more info check the detail list provided by Apple at:
Here!
Thursday, May 05, 2005
PooP's Tech World
VoIP seems to be doing a lot worse than it is helping us cheat the tel-cos out of the menial Long Distance charges . It is in secure - it is Traceable and worse of them all. It has no security protocol build into it. See this US Government Report about the state of the VoIP. Voice Over Internet Protocol is nice and dandy! But at what price? Loss of Privacy? Hackers penetrating more and more pf our private livess? What do you think?
Here is the ling to the Government's Reprot:
Wednesday, May 04, 2005
Firefox better than Safari?
Or at least, Al Fasoldt at the Newhouse News Service thinks so. In a column in the San Diego Union-Tribune, Fasoldt calls Safari "superb," but goes on to say that he's made Firefox his default browser anyway. In particular, he likes Firefox's bookmark management and its ability to save Web pages. (For what it's worth, I have them both on my Macs, and tend to go back and forth about equally.)
PooP's Tech World
The new document format appears to rival PDFs
The next version of Windows will include a new document format, code-named Metro, to print and share documents, Microsoft Corp. said yesterday. Metro appears to rival Adobe Systems Inc.'s PostScript and Portable Document Format (PDF) technologies.
Microsoft Chairman and Chief Software Architect Bill Gates demonstrated Metro during his keynote at the start of the Windows Hardware Engineering Conference (WinHEC) in Seattle.
Is PDF in danger? Not likely...
PooP's Tech World
If you updated to Mac OS X 10.3.9 last week, and are now having Safari issues..., you might want to check out this support page at: http://docs.info.apple.com/article.html?artnum=301380
from Apple. Java-enabled Web sites and Safari don't seem to get along after the update. According to Apple: "After updating to Mac OS X 10.3.9, some systems may have issues with Java applications and Java-enabled websites when using Safari.
PooP's Tech World
Firms Paid TV's Tech Gurus To Promote Their Products
The art of product placement, an increasingly popular and open practice with movie studios, has been handled quietly in television news. In the seemingly endless number of segments about the latest and greatest computers, cameras, music players and other gadgets, experts are praising products -- often on "satellite tours" of local stations -- without disclosing that the manufacturers are paying them to spread the word on the airwaves.
Since December, he has discussed Sony's ImageStation digital photo site on WNBC's "Today in New York" and Fox's "Arizona Morning"; Sony's DSC-H1 camera on "Good Day Dallas," "Today in St. Louis" and "News Daybreak" in Austin; Energizer E{+2} Lithium batteries on Fox's "Morning News at Seven" in North Carolina; Sony's Cyber-shot camera on Fox's Houston station, and Hewlett-Packard's Digital Entertainment System on "Today."
Payolls are back!
Monday, May 02, 2005
Lenovo completes acquisition of IBM's PC unit
Lenovo Group Ltd. announced yesterday that its acquisition of IBM's PC unit has been completed, saying the process was finished ahead of schedule.
I guess it is time to Stop buying the IBM Brand, unless they change the barnd name to Lenovo! And gues who would by a Lenovo brand? Not Many people, I guess.